Account Data Review – 8433505050, 4124235198, 8332218518, 2193262222, 9168399803
The account data review consolidates activity across 8433505050, 4124235198, 8332218518, 2193262222, and 9168399803 into a quantified map of transactions, frequencies, and variance. It emphasizes data quality, security controls, and measurable baselines for cross-account diagnostics. The report identifies recurring timestamps and spike events to establish stability and traceability. A cautious hold remains on interpretive conclusions, inviting further scrutiny to uncover underlying governance implications.
What Account Data Review Reveals About These Numbers
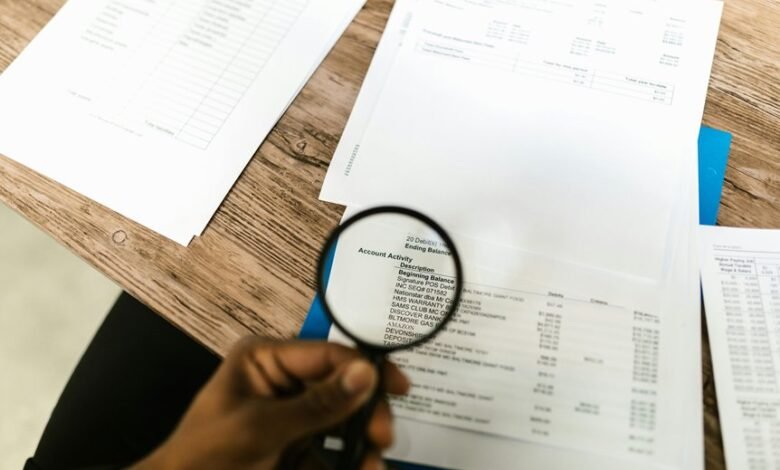
What the account data review reveals about these numbers is a precise map of activity patterns, transaction frequencies, and potential anomalies across multiple accounts.
The assessment emphasizes data quality and the rigidity of security controls, quantifying inter-account variance, recurring timestamps, and spike events.
Analytical metrics establish baseline behavior, enabling disciplined monitoring while preserving freedom to investigate irregularities without constraint.
How to Diagnose Anomalies Across the Five Accounts
Initial diagnostics focus on cross-account patterning, aggregating event counts, timestamps, and value anomalies to construct a consolidated anomaly profile for the five accounts.
The approach emphasizes anomaly detection within a governance framework, preserving data integrity and data lineage.
Key metrics include account hygiene, access controls, risk assessment, auditing practices, incident response, and change management to inform robust remediation decisions.
Practical Remediation to Improve Data Integrity and Security
Practical remediation focuses on concrete, measurable actions to restore and strengthen data integrity and security across the five accounts.
Systematic data governance clarifies ownership, scope, and metrics, enabling reproducible improvements.
Anomaly detection programs quantify deviations and trigger audits.
Data lineage maps trace transformations, while access controls enforce least privilege and revocation.
The approach is disciplined, transparent, and auditable.
Establishing an Ongoing Governance Framework for These Accounts
Establishing an ongoing governance framework for these accounts requires a structured, measurable approach that sustains data integrity and security over time.
The analysis quantifies roles, controls, and metrics, enabling objective assessment of account governance effectiveness.
Data stewardship responsibilities are delineated, with traceable approvals and periodic audits.
Compliance gaps are identified, prioritized, and closed through data-driven, transparent governance cycles crafted for freedom-oriented, rigorous accountability.
Frequently Asked Questions
What Is the Source of Each Account Number?
The sources of those account numbers vary by origin, with each tied to internal allocations and external vendors; provenance is tracked, access controls enforce boundaries, data freshness is periodically validated, and vendor impact assessed before integration into records.
How Often Is the Data Refreshed?
Data refresh cadence is every 24 hours. The system also supports ad-hoc refresh triggers when data integrity checks fail or critical events occur, ensuring timely updates. Analysts quantify latency, reliability, and trigger frequency to optimize performance for freedom-oriented users.
Who Has Access to the Data?
Access to the data is limited by defined access control policies; only authorized roles may view or modify it. Data provenance is tracked, enabling auditability and verification of user actions, ensuring accountable, measurable, and auditable disclosure and usage.
What Are the Data Retention Rules?
Data retention is governed by defined schedules and compliance requirements; data governance ensures periodic archival, deletion, or anonymization. The rules emphasize measured preservation, audit trails, and risk-based retention durations, enabling freedom while maintaining accountability over information lifecycles.
How Do External Vendors Influence These Accounts?
External vendors influence these accounts through access controls, data lineage, and refresh cadence, while enforcing retention policies and security compliance; juxtaposition reveals risk versus resilience, as quantified governance moderates exposure, ensuring freedom-oriented yet auditable data handling practices.
Conclusion
In the ledger of activity, these five accounts resemble a quiet constellation, each star aligned to a measurable cadence. The data map reveals precise inter-account variance and recurring timestamps like clockwork, punctuated by isolated spike events that demand scrutiny. With rigorous checks and quantitative baselines, anomalies recede into predictable shadows. The governance framework, once threaded through this tapestry, converts turbulence into actionable, data-driven discipline, preserving ownership, lineage, and the integrity of every transactional heartbeat.




